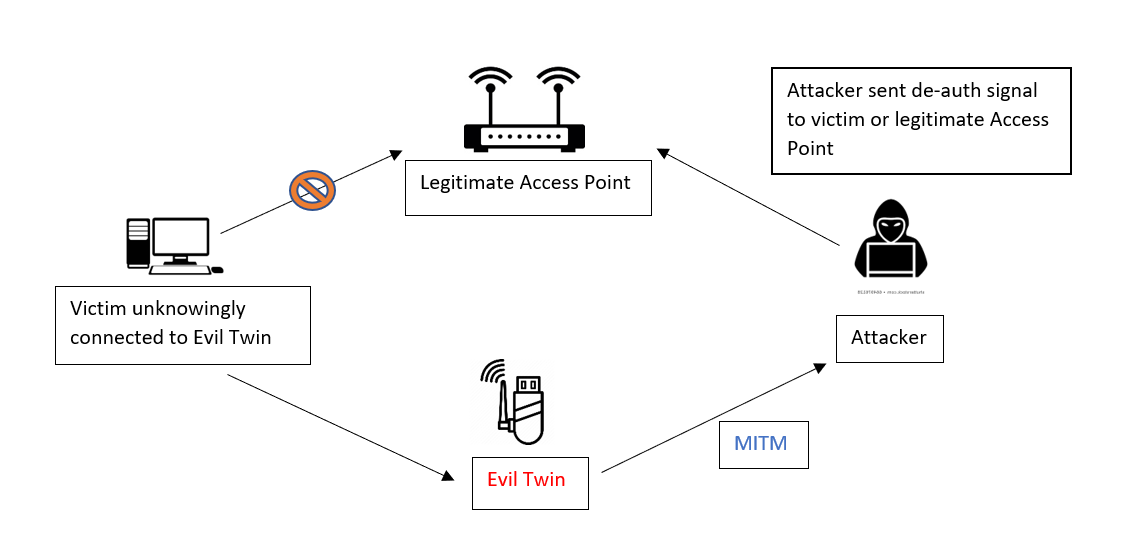
LM Evil Wifi is a powerful tool specifically designed for WiFi auditing, featuring advanced capabilities such as WiFi hacking and Evil Twin attacks. With its modified WiFi deauthentication firmware, it facilitates efficient execution of Evil-twin attacks. This software empowers users to conduct a range of tests and assaults on WiFi networks, ensuring comprehensive network security assessment. Its user-friendly interface promotes ease of use, enabling individuals to safeguard their WiFi networks by identifying and addressing potential vulnerabilities effectively.
Functions
- Deauther Attack : Disconnect 2.4G WiFi
- Deauther Beacon : Create fake networks
- Deauther Probe:Confuse wifi trackers
- Packet Monitor:Display wifi traffic
- Fake Access Point : For Evil Twin attack
Why did you use this?
For discovering vulnerabilities in your WiFi networks, utilize various WiFi attacks included in this device, such as deauthentication. Strengthen and secure your WiFi network to ensure the safety of your data and information within your home or office network
DISCLAIMER
This project serves as a proof of concept for testing and educational purposes related to WiFi hacking. Please use it exclusively on your own networks and devices. Prior to usage, ensure compliance with legal regulations in your country. We disclaim any responsibility for the actions taken with this program.
ATTACKS
Deauth
Closes the connection of WiFi devices by sending deauthentication frames to access points and client devices you selected. This is only possible because a lot of devices don’t use the 802.11w-2009 standard that offers a protection against this attack. Please only select one target! When you select multiple targets that run on different channels and start the attack, it will quickly switch between those channels and you have no chance to reconnect to the access point that hosts this web interface.
Beacon
Beacon packets are used to advertise access points. By continuously sending beacon packets out, it will look like you created new WiFi networks. You can specify the network names under SSIDs.
Probe
Probe requests are sent by client devices to ask if a known network is nearby. Use this attack to confuse WiFi trackers by asking for networks that you specified in the SSID list. It’s unlikely you will see any impact by this attack with your home network.
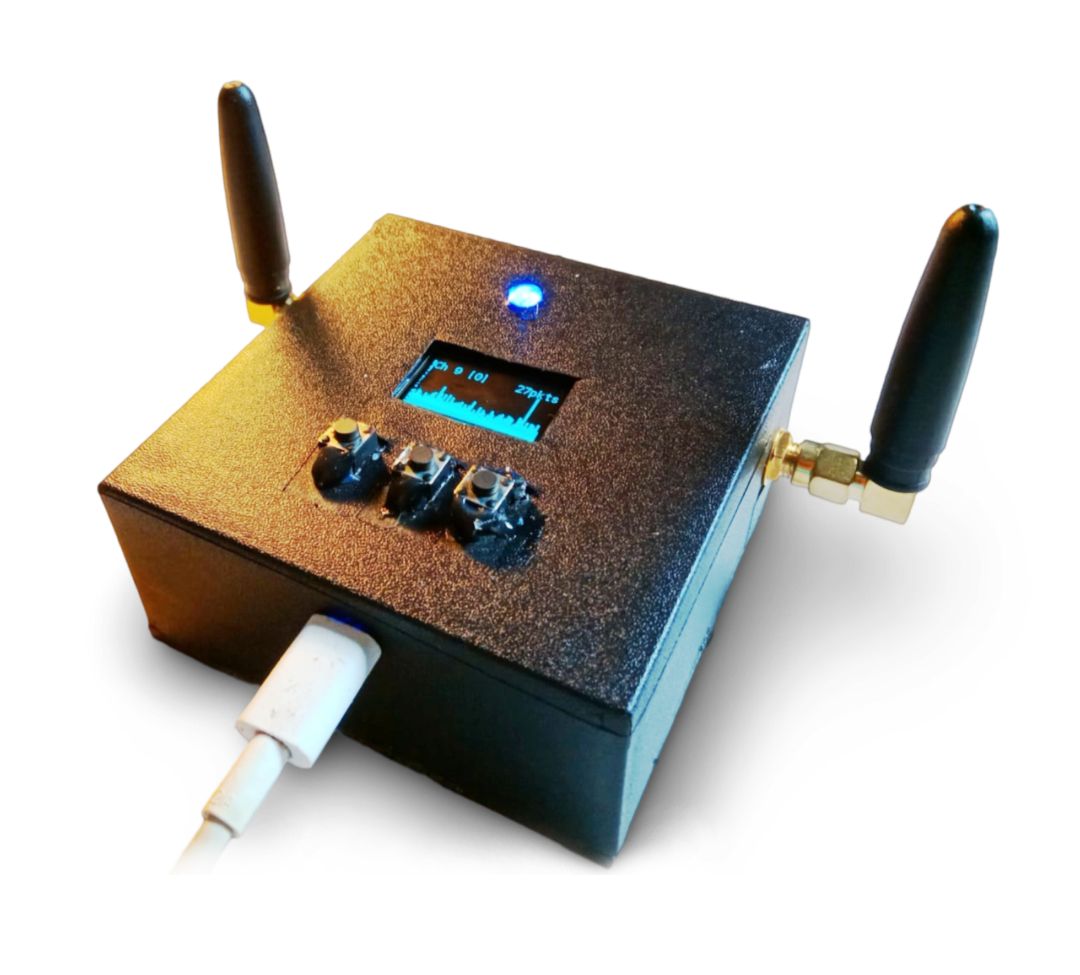
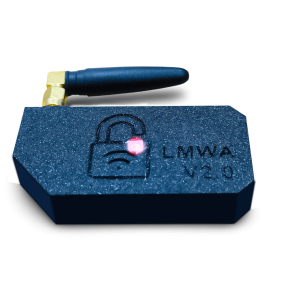
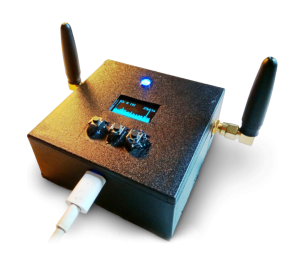
Technical Specifications
| Brand | LinkMe |
| Item Height | 38 Millimeters |
| Item Width | 60 Millimeters |
| LED Type | Neo Pixel |
| Item Weight | 2.5 Kg |
| Product Dimensions | 38 x 60 x 15 mm |
| Item model number | LM Evil Wi-Fi |
| Power | 5V – Micro USB |
| Color | Black |
| 3D Print Case | Yes |
| Functions | Scanner – WiFi networks and clients |
| Fake Access Point – For Evil-Twin attack | |
| Beacon flooding | |
| Probe flooding | |
| Deauthentication Attack | |
| Web Interface |